Evil Corp Switches to Ransomware-as-a-Service to Evade US Sanctions
Evil Corp—or at least a hacking group affiliated with it—is mixing things up.
Mandiant reports(Opens in a new window) that a threat actor it’s been tracking as UNC2165 appears to be related to the cybercrime group, which was sanctioned(Opens in a new window) by the US Treasury Department in 2019 for using “the Dridex malware to infect computers and harvest login credentials from hundreds of banks and financial institutions in over 40 countries, causing more than $100 million in theft.”
Those sanctions prevent organizations from paying a ransom to restore access to their systems. Financially motivated threat actors like Evil Corp aren’t targeting organizations for the fun of it, or looking to further a nation-state’s agenda, so they have to maximize their chances of getting paid. That means they need to make it harder for their victims to identify them.
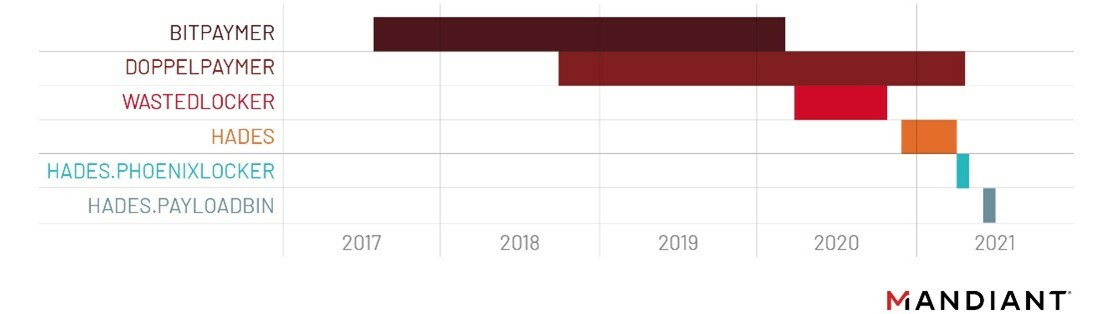
Which is why Mandiant says that hacking groups affiliated with Evil Corp have used a variety of ransomware strains over the last two years. The groups initially used WastedLocker(Opens in a new window), but after that ransomware’s connection to Evil Corp was revealed, they switched to a ransomware family known as Hades(Opens in a new window). Now they’ve started using a ransomware-as-a-service (RaaS) called Lockbit.
Mandiant says that using a RaaS offering makes sense for groups affiliated with Evil Corp:
Recommended by Our Editors
Both the prominence of LOCKBIT in recent years and its successful use by several different threat clusters likely made the ransomware an attractive choice. Using this RaaS would allow UNC2165 to blend in with other affiliates, requiring visibility into earlier stages of the attack lifecycle to properly attribute the activity, compared to prior operations that may have been attributable based on the use of an exclusive ransomware. Additionally, the frequent code updates and rebranding of HADES required development resources and it is plausible that UNC2165 saw the use of LOCKBIT as a more cost-effective choice.
The company says it expects similar groups “to take steps such as these to obscure their identities in order to ensure that it is not a limiting factor to receiving payments from victims.” Sanctions are unlikely to prevent ransomware gangs from going after more organizations, then, but at least they are making things more difficult for these cybercriminals.
More information about how Mandiant connected the dots between UNC2165 and Evil Corp as well as details about the hacking group’s operations is available via the company’s report.
Like What You’re Reading?
Sign up for SecurityWatch newsletter for our top privacy and security stories delivered right to your inbox.
This newsletter may contain advertising, deals, or affiliate links. Subscribing to a newsletter indicates your consent to our Terms of Use and Privacy Policy. You may unsubscribe from the newsletters at any time.


Comments are closed.