Hacker Gang DEV-0569 Found Using Google Ads To Push Ransomware Payloads
Microsoft recently warned that a known threat actor has updated its malicious ways by incorporating Google Ads into its operations. Besides malvertising on blogs and forums, DEV-0569, a threat group Microsoft has been tracking since August 2022, is now leveraging Google Ads to distribute malware payloads, including a new ransomware strain.
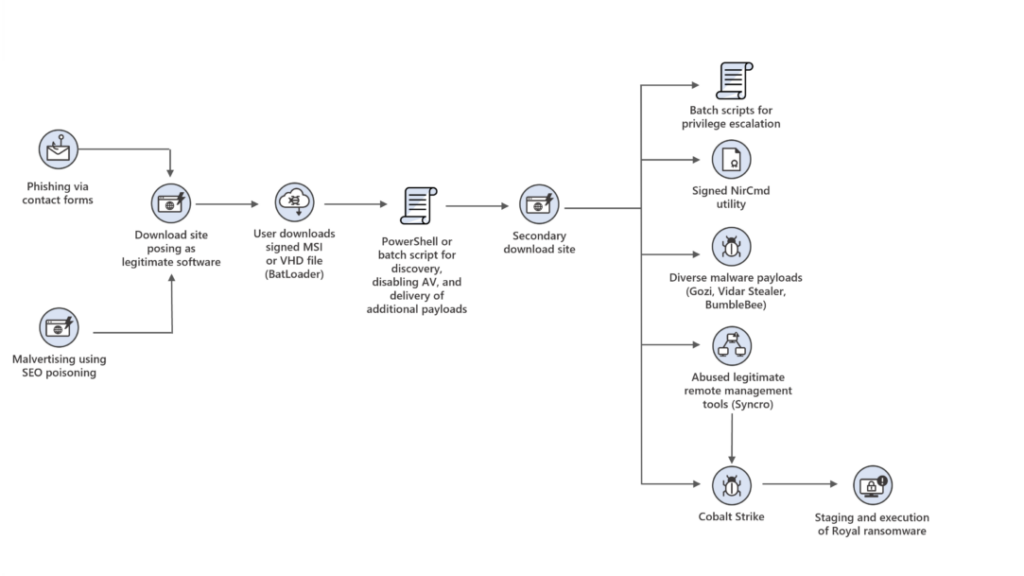
Microsoft observed upgrades to DEV-0569’s campaign in October 2022, a few months after identifying malvertising through phishing links or embedded updates sent in spam emails, posted on fake forum pages and blog comments. These links and updates redirected victims to BATLOADER, a malware downloader disguised as a software installer.
Hosted on the threat actors’ domain, BATLOADER tricks users into believing it is a legitimate downloader for applications like TeamViewer, Adobe Flash Player, Zoom, and AnyDesk, and software repositories from GitHub and OneDrive.
Instead of legitimate software, DEV-0569 pushes post-compromise payloads such as information stealers or a remote management tool to achieve persistence within the target network and disable antivirus products using the open-source tool NSudo.
However, Microsoft said DEV-0569 is now distributing the relatively new Royal ransomware since at least September 2022. Moreover, the threat group is now Google Ads for covert malvertising.
As an additional defense evasion technique, DEV-0569, like the operators of IceID malware, is now employing contact forms on targeted organizations’ websites to deliver phishing links since they can help bypass email-based protections.
“Observed DEV-0569 attacks show a pattern of continuous innovation, with regular incorporation of new discovery techniques, defense evasion, and various post-compromise payloads, alongside increasing ransomware facilitation,” Microsoft noted.
“These methods allow the group to potentially reach more targets and ultimately achieve their goal of deploying various post-compromise payloads. DEV-0569 activity uses signed binaries and delivers encrypted malware payloads.”
See More: 250 U.S-Based Websites, Including News Agencies, Infected as TA569 Compromises the Ad Supply Chain
DEV-0569 Infection Chain | Source: Microsoft
Royal ransomware is a new strain with private operations. It doesn’t operate under a ransomware-as-a-service model, recently got its own encryption mechanism, and demands anywhere between $250,000 and over $2 million as ransom upon successfully victimizing a target.
For more details on Royal ransomware, refer to cyber threat intelligence company SecurityScorecard’s technical analysis.
“DEV-0569 will likely continue to rely on malvertising and phishing to deliver malware payloads,” Microsoft continued. “Since DEV-0569’s phishing scheme abuses legitimate services, organizations can also leverage mail flow rules to capture suspicious keywords or review broad exceptions, such as those related to IP ranges and domain-level allow lists.”
Let us know if you enjoyed reading this news on LinkedIn, Twitter, or Facebook. We would love to hear from you!
Image source: Shutterstock


Comments are closed.