How to Stop Ransomware: Breach Prevention vs. Cobalt Strike Backdoor
With a year-on-year increase of over 161%, malicious usage of cracked versions of Cobalt Strike (a legitimate penetration test tool) is skyrocketing. For organizations that still rely on signature-based next generation antivirus (NGAV) solutions to protect their endpoints from ransomware and other advanced attacks, this is terrible news.
Developed in 2012 to give pen testers and red teams the capability to conduct hard-to-spot test attacks, Cobalt Strike is designed to be dynamic and evasive. Its purpose is to simulate advanced malware delivery and deployment. While these capabilities have made it an invaluable red team tool, malicious operators have hijacked various versions of Cobalt Strike, re-engineering it into a devastating malware delivery platform that can lead to ransomware.
Over the years we have seen cybercriminals use Cobalt Strike to facilitate a range of threats, including attacks on point of sale systems. In 2020, 66% of all ransomware attacks used Cobalt Strike. The platform was also used in last year’s SolarWinds attack. With the average ransom now exceeding $240,000, and remediation costs soaring beyond $4 million, a malicious Cobalt Strike attack can be devastating for any business.
The good news is that Cobalt Strike cannot evade Morphisec’s unique Moving Target Defense (MTD) technology. In this blog post, I will explain why Cobalt Strike is so dangerous, why NGAV solutions are unable to stop it, and how MTD can defeat these attacks — referencing a recent investigation report from a Morphisec client.
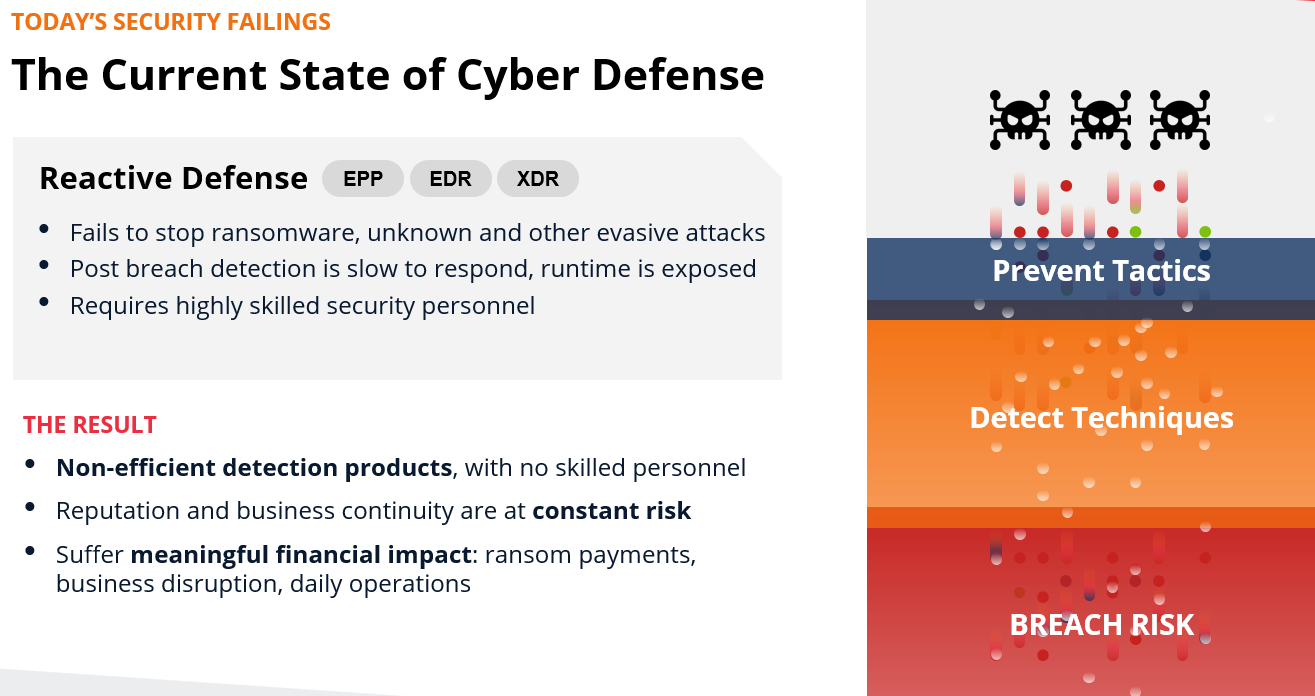
Why NGAV Solutions Fail to Stop Cobalt Strike
Looking at a typical Cobalt Strike attack chain, we can see how it slips past standard organizational security controls.
Threat actors use Cobalt Strike to gain control of an endpoint or a server while maintaining a very low footprint. Compared to installing a 3rd party remote connection service like TeamViewer, Cobalt Strike allows almost invisible remote access for malicious actors. Attacks using Cobalt Strike can start from various vectors ranging from phishing emails to known server vulnerabilities and misconfigurations.
The goal for any Cobalt Strike attack is the deployment of a post-exploitation payload, known as a “Beacon,” onto a compromised endpoint. While some Cobalt Strike attacks can involve executables such as DLL files or libraries being installed on a targeted endpoint, most work by injecting malicious shellcode into legitimate processes. With Cobalt Strike payloads uniquely generated for specific victims and hidden within innocent processes and applications, antivirus solutions that rely on recognizable malicious signatures cannot see or stop them.
Because Cobalt Strike shellcode can move via the named pipes used for inter-process communication within Windows and Unix machines, malicious shellcode will remain invisible even when an antivirus or endpoint detection and response (EDR) solution uses a sandbox — unless it is configured to emulate named pipes (which is rare).
Although Cobalt Strike is a command and control (C2) framework, which means that attacks rely on attackers establishing communication with clients installed on targeted machines, analyzing network traffic is not a reliable way of finding and stopping Cobalt Strike Beacons.
The reason why is simple: the way in which Cobalt Strike conducts network egress is highly customizable and capable of mimicking traffic from legitimate applications. This feature of the Cobalt Strike platform called “Malleable C2” allows attackers to adapt command and control traffic (C2) to the kind of legitimate traffic that is likely to come from an uncompromised victim device. As a result, threat actors can configure Cobalt Strike to blend in with background noise, making traffic-based detection far more difficult. Critically, the stagers (programs that can be used to download sections of the Beacon payload) that Cobalt Strike uses to download the Beacon payload deploy mostly in device memory. Consequently, this stage of an attack is completely hidden from antivirus solutions that do not scan device memory.
Once an individual endpoint has been compromised, Cobalt Strike is designed to allow attackers to move laterally within a victim’s network. Integrated with tools like Mimikatz, threat actors can then use Cobalt Strike to find and exfiltrate credentials and run remote commands. All the while, because Cobalt Strike can use named pipe pivoting, only a single endpoint needs to be connected to the outbound web–with the ability to communicate with the threat actors–for an entire suite of compromised machines to be exploited.
During our incident response work, we have seen multiple examples of threat actors exploiting vulnerabilities to allow further lateral movement during Cobalt Strike attacks. We have come across misconfigured update servers, file storage servers, and even endpoint workstations acting as the egress point for outbound communication.
On a practical level, Cobalt Strike is also a well-documented and readily available attack platform. This means that using cracked versions of it is relatively straightforward even for middle-of-the-road threat actors.
The factors above make Cobalt Strike a highly dangerous threat and one that NGAV solutions, as well as many endpoint protection platforms (EPP) and EDR products, may not be able to stop.
Moving Target Defense Defeats Cobalt Strike

When misused by cybercriminals, Cobalt Strike is an immense threat that most organizations are ill-equipped to defend against. Nevertheless, although Cobalt Strike attacks are highly obfuscated and dynamic, not to mention capable of avoiding signature-based solutions, stopping them IS STILL POSSIBLE.
Preventing Cobalt Strike attacks without straining resources requires a solution that constantly protects device memory and is not reliant on monitoring and repeated scanning.
Proactive and autonomous, Morphisec does this through our Moving Target Defense technology. This means that rather than playing hide and seek with an already ongoing attack, our solutions morph device memory, luring and trapping fileless and in-memory attacks like Cobalt Strike before deployment even happens. Critically, Morphisec can do this even with attacks that have already begun prior to Morphisec being installed. For one of our clients in the financial industry, this capability became apparent soon after they started working with us.
A Cobalt Strike Success Story
Our customer, a highly regarded boutique financial institution, quickly and easily installed Morphisec Guard’s lightweight agents on their endpoints. Four months later, Morphisec stopped a Cobalt Strike backdoor attempt that had originated prior to the installation of Morphisec Guard from a Gootkit malware on one of the client’s Windows 10 terminals shared access devices. A few days later, we accessed the device and performed a preliminary analysis on the persistence of the threat.
Here is what we found:
- Morphisec Guard automatically prevented a persistent Cobalt Strike backdoor that executed each time a user logged into the compromised device. Lying dormant in between login attempts, the backdoor had been in place on our client’s device since early August.
- Because the attack began several weeks before Morphisec had been installed, there was a possibility that attackers may have accessed the backdoor before our solution was in place.
- Although the customer had several market-leading, NGAV solutions installed, including a suite of network and gateway solutions and an advanced EDR solution, none of them spotted the attack.
- The backdoor was installed for three months without any signature update from the client’s NGAV or EDR solutions. It was only after Morphsiec detected, stopped, and shared details about this backdoor with the AV community that other solutions were able to update their signature libraries.
Since the customer is in a highly regulated industry, and there was a possibility that attackers might have accessed the backdoor between the time of infection, they may have had to invest further resources in estimating the risk this security lapse created. Fortunately, Morphisec also offers a range of on-demand and retainer-based incident response offerings to help mitigate this risk. These services can be used whenever required, as well as when deploying Morphisec’s Moving Target Defense solution.
Ultimately, however, our client’s experience shows not only that Morphisec’s unique Moving Target Defense technology can prevent Cobalt Strike attacks, but also that our solutions can prevent persistent threats even if an endpoint or server is already compromised. Morphisec takes the features that make Cobalt Strike dangerous, like its obfuscated shellcode, Malleable C2, and lateral movement, and makes them completely redundant. In this way, Morphisec can help prevent the serious consequences resulting from a malicious Cobalt Strike attack that can lead to ransomware and other cybercrime damage.



Comments are closed.