Ransomware-Wielding Criminals Increasingly Hit Healthcare
Industry Specific
,
Targeting Healthcare
,
Video
Sector Especially Vulnerable Due to Dispersed IT Footprint, Massive Records Storage
Ransomware-wielding criminals continue to seek ransoms from healthcare sector victims.
See Also: Finding a Password Management Solution for Your Enterprise
But most if not all ransomware-wielding attackers aren’t out to amass healthcare victims, per se. Experts say shotgun-style attacks remain common, in which attackers attempt to hit many different organizations at once, often via malware-laden phishing emails or stolen remote access credentials, and then see what they’ve caught in their net and might want to pursue.
This strategy typically snares less well-prepared organizations, experts say, adding that this often means healthcare sector players.
A survey of 318 healthcare organizations across 31 countries conducted early this year by research agency Vanson Bourne for Sophos found that 66% reported being hit with ransomware.
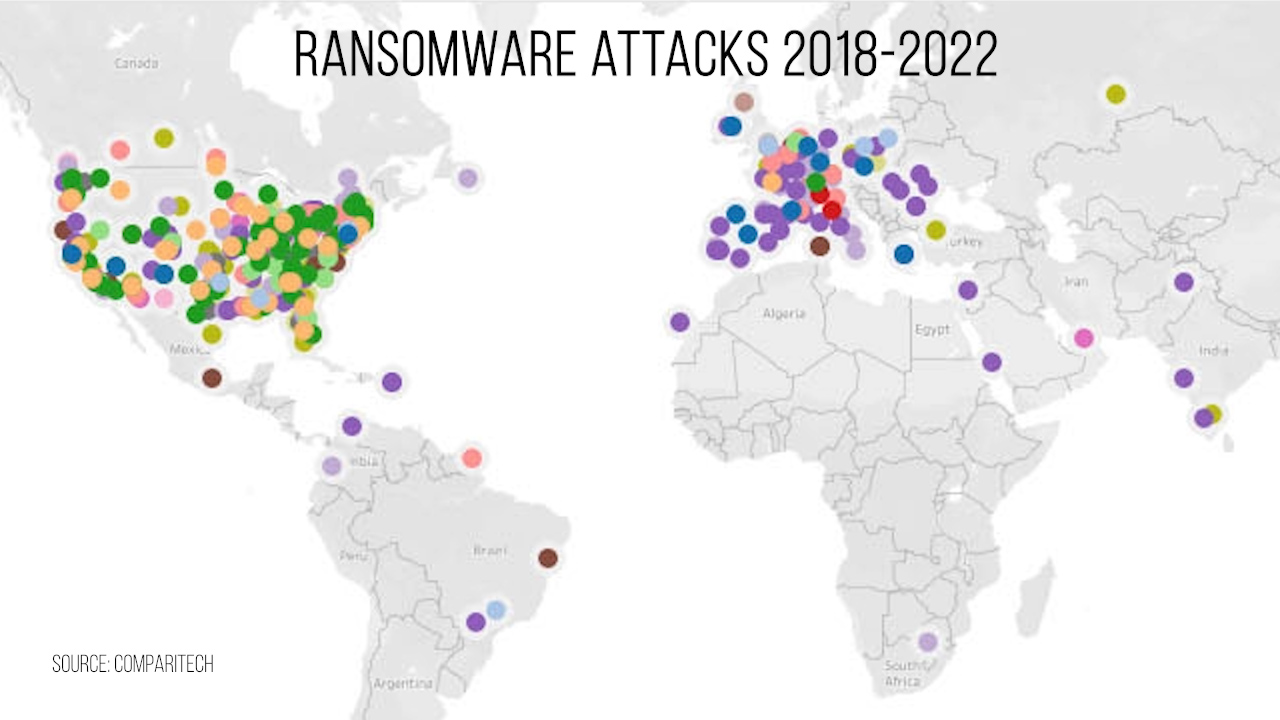
Since 2018, there have been 500 publicly confirmed ransomware attacks on healthcare organizations worldwide, according to Comparitech. Its new report finds that attackers have hit nearly 13,000 separate facilities affecting almost 49 million patient records. The total estimated cost of these attacks exceeds $92 billion in downtime. Ransomware payments to hackers are estimated at nearly $44 million.
“When it comes to healthcare, some of the ransomware attacks that are happening are moving away from the larger, more protected organizations and toward the smaller, less protected – like clinics and those types of organizations, and very small rural hospitals, that may not have the infrastructure in place to help prevent these kinds of attacks,” says Denise Anderson, president and CEO of the Health Information Sharing and Analysis Center.
Why Healthcare Is So Vulnerable
Even larger healthcare entities are particularly vulnerable to ransomware attacks. Hospitals can’t just close up shop for a few weeks while systems get restored. Instead, they have an imperative to remain operational and restore systems as quickly as possible, while continuing to care for patients.
Per the CIA pyramid or triad often used to guide information security programs – comprising confidentiality, integrity and availability – “organizations attacked by ransomware groups are often targeted on the C – confidentiality – and the A – availability – of the CIA pyramid,” says John Fokker, head of threat intelligence for the Advanced Research Center at Trellix.
“Unfortunately, healthcare organizations can be impacted both on their availability through an encrypting attack and on their confidentiality through data theft and leak extortion, due to their HIPAA compliance,” he says.
Numerous hospitals large and small continue to fall victim to ransomware attacks, such as CHSF Hospital Center in Corbeil-Essonnes, near Paris. In August, the hospital’s IT, medical imaging and other systems were all disrupted for weeks, and the attackers demanded a ransom in cryptocurrency worth millions of dollars, which the hospital declined to pay.
For defenders, challenges abound. For starters, a healthcare organization’s IT footprint tends to be widely dispersed, oftentimes across multiple sites as well as different types of systems, including kiosks.
“The actual architecture of a healthcare organization tends to be more challenging than a normal company,” says Bill Siegel, co-founder and CEO of ransomware incident response firm Coveware. If a business gets hit by ransomware and 100 laptops get crypto-locked, oftentimes IT can simply replace the laptops. In a hospital, that’s often not the case.
Another complication: The electronic health record systems on which hospitals rely are inherently large and difficult to manage, both in terms of the database they use to track files as well as the extremely large files they keep for images X-rays, CAT scans and more, which can be difficult to keep backed up.
“Because all the doctors, all the facilities have to have access to a very, very large data store, that’s very cumbersome to back up and move around, and in turn can be quite susceptible to attack,” Siegel says.
Network topology can also be a factor. “Healthcare IT and operational technology – OT – systems are often mixed – flat network – for ease of use, and not strictly segmented as in the industrial world,” Trellix’s Fokker says. “This means that the impact of a ransomware attack will be enormous as mission-critical systems, with all their OT challenges, are reachable via the corporate IT network, making it child’s play for a threat actor to paralyze the organization.”
Ransomware: Top Attack Vectors
Ransomware-wielding attackers often mix a variety of tactics for hitting targets. Beyond phishing emails, Fokker says other common tactics include “active scanning” for known vulnerabilities in software, credential access, referring to stealing usernames and passwords – for example, via man-in-the-middle attacks or brute-forcing – as well as “piggybacking on commodity malware and/or purchasing access via initial access brokers.” Such access is often achieved using stolen remote desktop protocol or VPN credentials.
The typical boilerplate for a notice of a security incident issued by a victim points to sophisticated attackers having evaded the organization’s defenses. But Peter Mackenzie, the director of incident response at Sophos, says most ransomware attacks are anything but advanced. “It is depressing how amateur some of these attacks are, but they work,” he says, adding that attackers sometimes watch YouTube videos to learn how to use highly automated tools.
Attackers often hit a large number of organizations and then see who has fallen victim and who they want to pursue further, experts say. Historically, some attack groups would not extort healthcare targets, sometimes offering a “free” decryptor instead, given the bad publicity such attacks generate. Even then, of course, the disruption and damage might already be severe.
“If they get the decryptor tool for free, they’re still going to be wildly disrupted and have a lot of risks toward patient care, because restoration processes are going to be extremely painful and time-consuming,” Siegel says. After Ireland’s Health Service Executive was hit by Conti in the spring of 2021, for example, patient care in the country was disrupted for months while it recovered, even though Conti had given HSE a decryptor.
While extorting healthcare organizations used to be at least somewhere avoided, experts have recently been tracking a surge in groups that don’t filter out healthcare organizations that they’ve caught in their net – presumably because they’re trying to make up recent shortfalls in revenue (see: Ransomware: ‘Amateur’ Tactics Lead Fewer Victims to Pay).
“During the COVID-19 pandemic, we observed several groups avoiding attacks on the healthcare sector,” Fokker sys. “However, with the current geopolitical climate, it seems that Western healthcare organizations are fair game for the threat actors once more.”
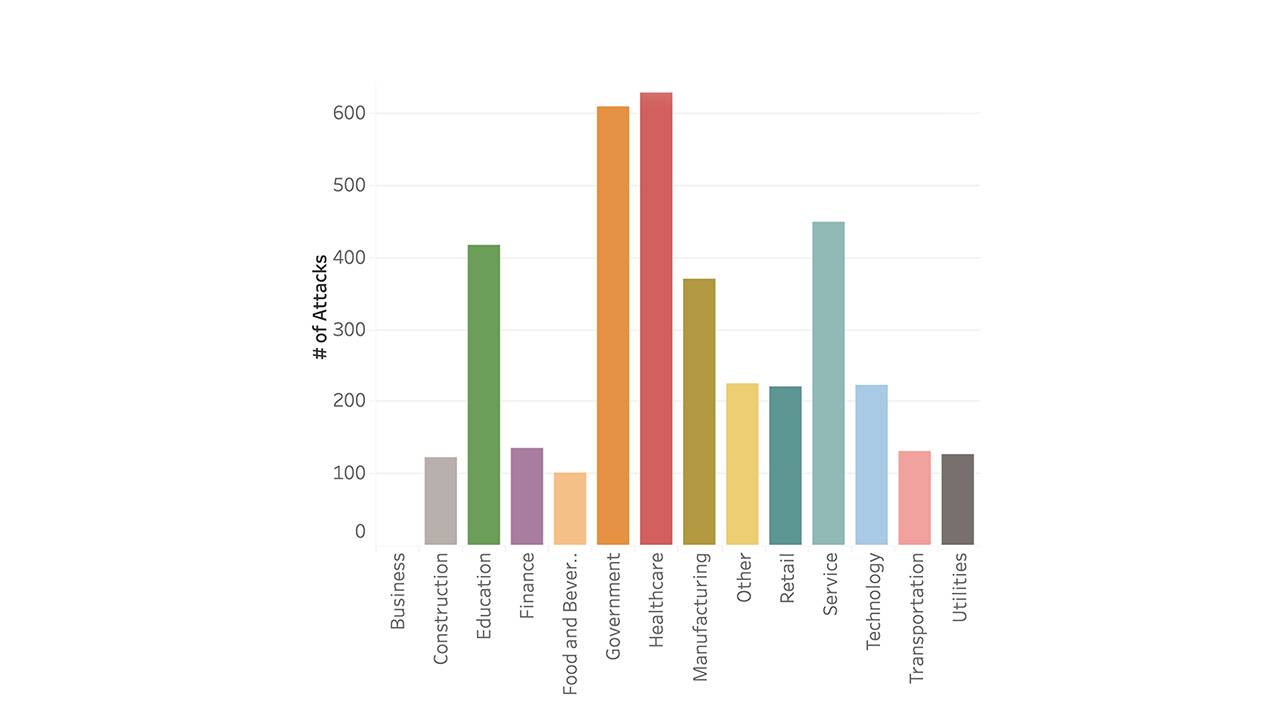
Based on thousands of incidents with which it assisted from July through September, Coveware says 17% involved healthcare – just behind professional services at 18%, making it the second-worst sector affected by ransomware. The attacks on healthcare have been increasing too, compared to previous quarters, which the firm attributes in part to a rise in activity tied to the Hive ransomware group, which doesn’t hesitate to hit healthcare.
Other ransomware groups also don’t shy away from targeting healthcare. According to joint security alerts issued by the FBI and the Cybersecurity and Infrastructure Security Agency, Zeppelin, Karakurt and Daixin continue to count numerous healthcare victims (see: Security Alert: Daixin Ransomware Targets Healthcare).
Monetizing Healthcare Hits
Once healthcare organizations fall victim to ransomware-wielding criminals, experts say they will typically attempt to monetize these attacks using two interrelated strategies: encrypting data and extorting victims for the promise of a decryption tool, as well as stealing data. Wielding the stolen data, attackers can try to force a ransom payment for the promise of returning it safely – and deleting all extra copies. But experts say that whatever they promise, expect them to sell the data to underground cybercrime forums.
“Patient data is still really valuable,” says Allan Liska, a principal intelligence analyst at Recorded Future. “It is going to be very sellable in underground markets, and the Chinese government in particular loves to buy medical records.”
How many organizations fall victim to ransomware – in the healthcare sector or otherwise – remains unclear. Law enforcement agencies say underreporting is rampant.
Gauging the extent to which organizations are falling victim to ransomware attacks remains difficult. Many ransomware groups run data leak sites, where they attempt to name and shame nonpaying victims into paying. If they don’t pay, the attackers often leak stolen data to try and scare future victims into paying.
One measure of the number of organizations falling victim to attacks is to count who shows up on a data leak site. But this is imprecise. Gangs don’t list all victims, and sometimes they list the wrong victim or even claim false victims to build up their reputation.
Counting the number of victims who appear on data leak sites at least provides a benchmark. Liska says that for healthcare in 2020, data leak sites listed 185 healthcare victims, and the number rose to 285 in 2021. This year, up to the end of October, ransomware groups’ leak sites listed 180 victims. “So we’re going to be ahead of 2020 numbers, but not hitting 2021,” he says.
Again, however, these numbers have to be taken with a grain of salt. For example, in July, the FBI and CISA released a report warning that since at least May 2021, North Korean state-sponsored attackers had been using Maui ransomware to target the healthcare and public health sectors. The report did not identify victims or quantify how many organizations had fallen victim (see: Feds Warn Healthcare Sector of ‘Maui’ Ransomware Threats).
“So there may be a lot more happening with healthcare that we don’t know about, perhaps more so than even in previous years, at least in the U.S.,” Liska says.

Over 5,000 health data breaches since 2009 have affected the personal information of 370 million people. Ransomware gangs and hackers are targeting healthcare providers, insurance firms and partners at an alarming rate. Targeting Healthcare explores these trends and how the industry can respond.


Comments are closed.