How can organizations be prepared in the event of a ransomware data disclosure?
Ransomware denies a user or an organization access to their files or systems. A ransomware attacker encrypts files on the system and demands ransom from the user or organization to decrypt the files and restore access. Many ransomware attackers do not simply encrypt files with ransomware payloads to hold for ransom but also spend time secretively collecting and exfiltrating files from a compromised network after achieving sufficient access before encrypting files.
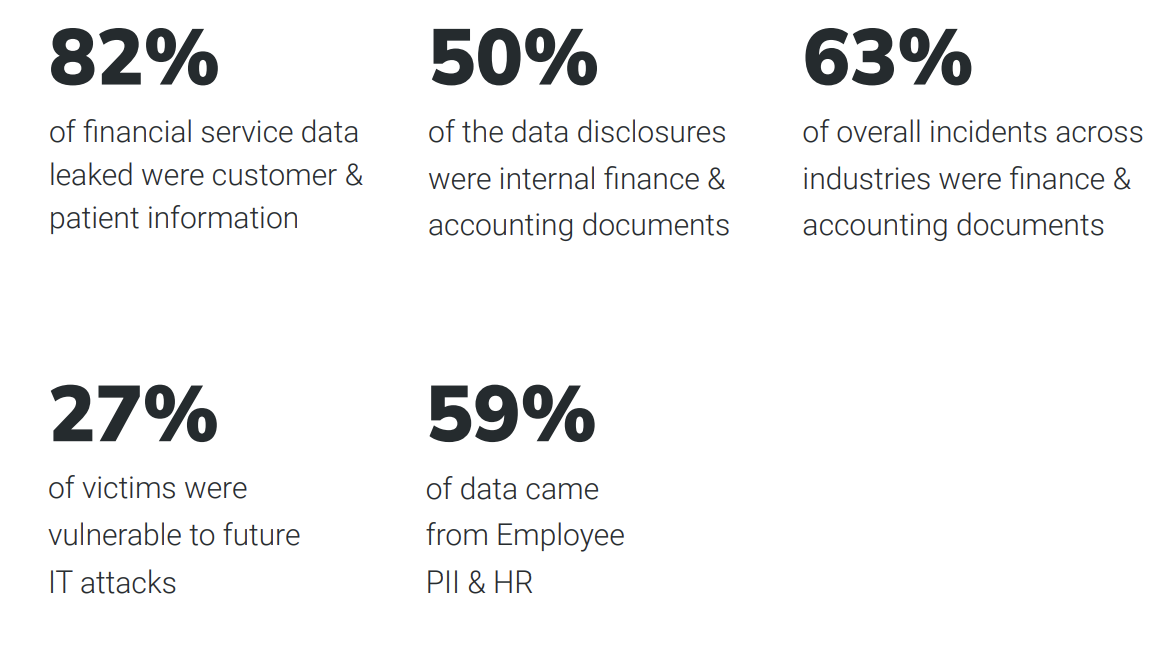
A report by Rapid7 analyzed separate data disclosures between April 2020 and February 2022 that aimed to press victims to pay ransoms and identified several trends in the data. In this article, we shall discuss the ransomware data disclosure trends and how to safeguard files from ransomware attacks.
Ransomware data disclosures
Ransomware data disclosures usually take place in two stages.
- In the first stage, a sample of compromised data is released to make the threat credible to victims and to make them realize the possible damage further disclosure would cause them. By this time, attackers would have given the victim the first opportunity in private to pay the ransom. Refusal to pay ransom prompts the attacker to place additional pressure on the victim in a public manner.
- In the second stage, the attackers choose to disclose or sell more or all of the previously unreleased data in their possession because the victim still refused to pay the ransom for the attack.
As per the report, upon analyzing the record types included in the data disclosures, it was observed that generally, financial and accounting data was disclosed in most double extortion incidents. Customer data and employee data were the next popular interests for ransomware attackers.
Data disclosure trends by industry and threat actors
The below image shows the distribution of ransomware incidents across industries and countries.

According to the report, 12% of disclosure comprised intellectual property, which is usually rare, except in the pharmaceutical industry, where it accounted for 43% of the disclosures investigated. Customer information is mostly targeted in Financial Services than other types of data. 63% of data leaked was financial, the most commonly leaked data in general, followed by customer/patient data 48%.

Among the private sector organizations, the Financial Services industry is uniquely security-centric. Its existence depends heavily on the perceived trustworthiness and its ability to protect customer data and funds. The Customer & Patient Data appearing more frequently in these disclosures indicates that the attackers aim to put greater pressure on victims with more severe legal and regulatory consequences of patient data breaches. A more detailed and granular patient data proves much more useful to criminals for identity theft and other forms of fraud.
It was also observed that the leaked data varied by threat actor group. Some of the ransomware groups have a distinctive profile in the categories of files they would choose to include in their disclosure.

How can organizations be prepared against ransomware attacks?
Ransomware attackers tend to choose their targets carefully to maximize their profits and reduce their risks and labor requirements. They are more interested in targets that seem more lucrative, easier to compromise, more likely to pay ransoms, and more suitable for short-term extortion than long-term data collection, depending on the type of data they possess. The sensitivity of each type of data is different for different industries, and different ransomware groups may find some types of data more sensitive than the others.
Here is what security professionals can do to safeguard information from ransomware attackers.
- Backups are the best line of defense against the file encryption layer, as organizations can easily restore files and will not have to pay ransoms to retrieve their files.
- Backups cannot protect against data disclosure. The best defenses against data disclosure are – file encryption for rendering files unreadable to unauthorized people; and network segmentation which will reduce the lateral movement of attackers into the infrastructure containing key data assets, including backups.
- Based on the frequency with which they appear in relevant data disclosures, organizations can assess which specific data assets require additional protection like file encryption and network segmentation.
- Organizations must be prepared on what steps to take in the event of a ransomware data disclosure. The data disclosure trends discussed earlier can help organizations prepare their action plans. For example, a bank or a hospital that faces a ransomware attack must be able to anticipate that any data disclosure is likely to contain customer/patient data and take action appropriately.
Image and source credits: Rapid7
Read next: Top eight cybersecurity predictions for 2022-23 by Gartner


Comments are closed.