Why Do Ransomware Attackers Use Bitcoin?
The demand for Bitcoin has increased over the last decade among traders and criminals alike. Ransomware attackers like REvil, DarkSide, Petya, and Bad Rabbit have been haunting the business community for a while.
Such attackers use cryptocurrency because it is speedy, sometimes hard to trace, keeps users anonymous, and beyond any government’s laws or regulations.
The question a lot of us have is, why Bitcoin?
Why Would Someone Choose Bitcoin Ransom Over Other Cryptocurrencies?

Bitcoins are traceable, which makes asking for Bitcoin ransom seem counterintuitive. Cybercriminals want their transactions to be as easy and speedy as possible. One of the major impediments to their plans could be the lack of availability of their demanded currency.
Bitcoin is freely available in almost every region that has internet access and exchange, while other currencies have their limitations in terms of availability.
If a currency is not available to the payer, it is no use how untraceable or sneaky it is because it would delay the transaction and increase the risk of authorities catching up.
How Criminals Evade Bitcoin Tracing

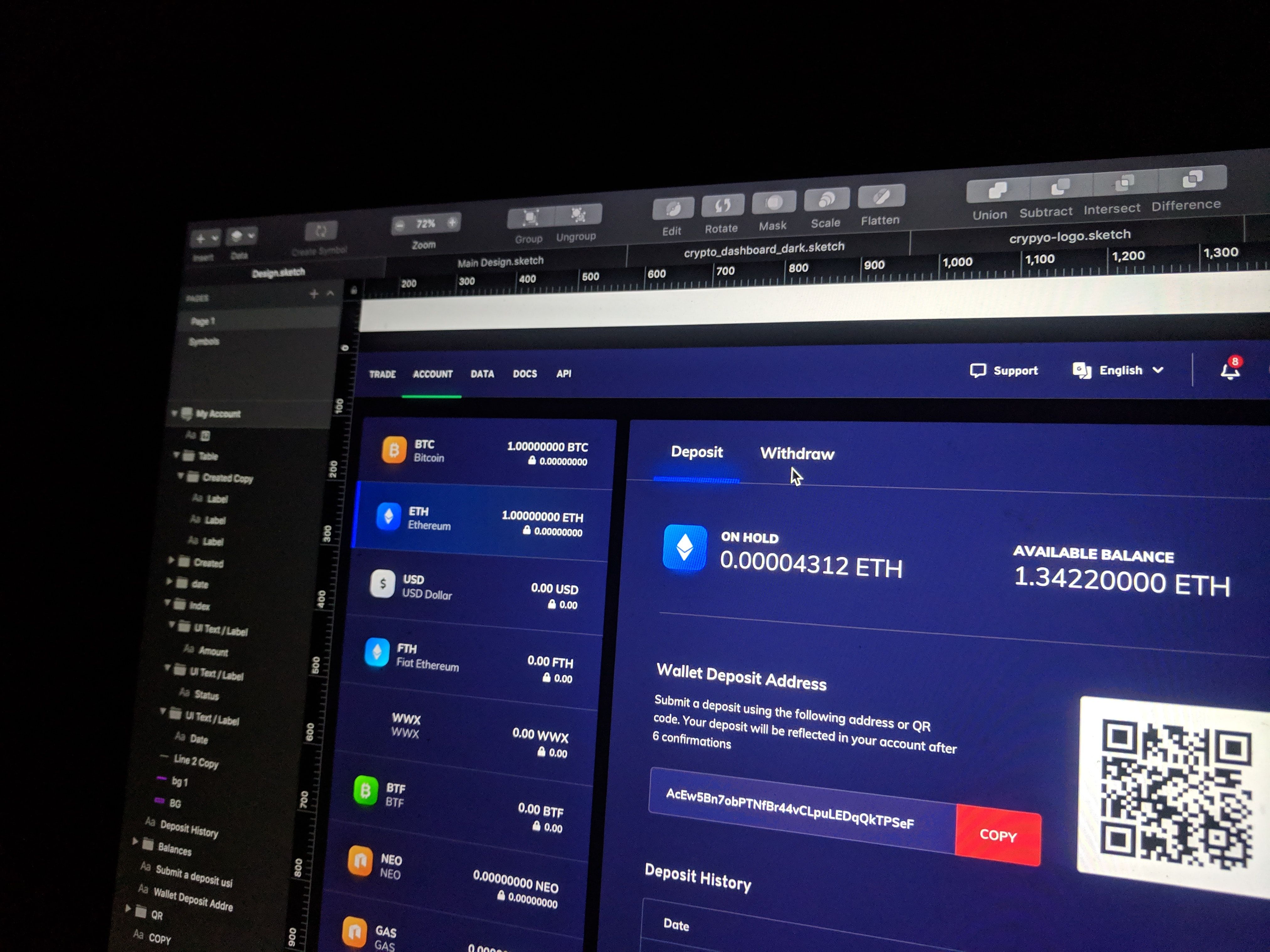
While Bitcoins are traceable, the wallets that keep Bitcoins are anonymous. The most you need to open a wallet is an email address.
The fact is that you can trace the movement of Bitcoin and figure out which accounts the specific Bitcoins end up in, but that won’t give you the identity of the account holder. With mixing services jumping in, you lose any trail the attackers might leave.
Bitcoin mixers take the ransom and mix it with other funds they receive from other users in one account. Then, they return those amounts of funds to the users and the attackers.
If you know how Bitcoin works, you’re probably aware that each Bitcoin has an ID or hash that helps you figure out its history of transactions and trace its movement. When tracing ransom Bitcoins, their ID and hashes are what investigators look at.
Once mixed with other funds and redistributed, the Bitcoins originally given by the victims end up in several irrelevant accounts while attackers get away with the same amount of currency. This looks ingenious and helps many ransomware attackers get away, but it isn’t entirely foolproof.
One of the ways you can trace the attackers is by looking at the pattern of transactions. If the attacker is not an expert, the number of Bitcoins will add up somewhere down the line. It can be hard and tricky, but not entirely impossible. Plus, cashing Bitcoins requires some verification since banks don’t cater to anonymity.
So if you’re close enough in tracing and following the patterns, you’ll find out who cashed the exact amount you’re looking for. If the attacker happens to be from or in another country, state, or nation, you might have to prove their crime to their government, which could be impossible in some countries because:
- That country’s courts might not regard blockchain-based evidence as substantial.
- Even if they do, you lose their traceable evidence at the mixer.
Beef Up Your Defenses Against Ransomware
With the shift to remote work, the risk for ransomware attackers to exploit individuals and organizations has increased manifolds. However, there are several measures you can take to counter the onslaught of ransomware attackers.
- Use a good firewall
- Take and update multiple back-ups frequently
- Learn about your system and its accessibility points
- Train your workforce to prevent unauthorized access
- Implement a Zero-Trust security model
- Educate your employees about phishing techniques
- Scan every foreign software and device before letting it into your system
By taking these measures, you can ensure the safety of your data and protect your network against ransomware.
Read Next
About The Author



Comments are closed.